Sad to say, it may possibly with MD5. In truth, back again in 2004, researchers managed to generate two distinct inputs that gave exactly the same MD5 hash. This vulnerability is usually exploited by undesirable actors to sneak in malicious facts.It absolutely was developed by Ronald Rivest in 1991 and is primarily used to validate facts integrity.
 Amanda Bearse Then & Now!
Amanda Bearse Then & Now! Marcus Jordan Then & Now!
Marcus Jordan Then & Now!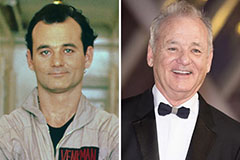 Bill Murray Then & Now!
Bill Murray Then & Now! Morgan Fairchild Then & Now!
Morgan Fairchild Then & Now! Megyn Kelly Then & Now!
Megyn Kelly Then & Now!